AppArmor, a powerful security module for Linux systems, provides an array of features to enhance the control and security of applications running on an Ubuntu operating system. In this guide, we will focus on how to enable or disable AppArmor on Ubuntu 22.04 or 20.04. Managing AppArmor effectively can significantly bolster your system’s defense mechanisms against various security threats. Here’s a quick glance at some key features of AppArmor and the benefits of toggling it on or off:
- Enhanced Security: AppArmor allows for the setting of program-specific profiles, limiting the capabilities of applications and thereby reducing the risk of security breaches.
- Flexibility: Easily switch AppArmor on or off to suit your security needs or to troubleshoot software compatibility issues.
- User-Friendly: Unlike some other security tools, AppArmor balances robust security with user accessibility, making it easier for administrators to manage application permissions.
- Compatibility: It seamlessly integrates with many common applications and services, ensuring a smooth operation of your Ubuntu system.
Understanding how to control AppArmor’s functionality is a vital skill for Ubuntu users, particularly system administrators and IT professionals who prioritize system security. Let’s dive into the steps required to enable or disable AppArmor, enhancing your Ubuntu system’s security according to your specific needs.
Pre-Steps Before Managing Apparmor on Ubuntu 22.04 or 20.04
Install Additional Apparmor Packages
To fully leverage AppArmor’s capabilities, ensure that the apparmor-utils package is installed on your system. This package is essential as it provides various commands necessary for managing AppArmor effectively.
Begin by opening your terminal and executing the installation command:
sudo apt install apparmor-utils apparmor-notify apparmor-profiles apparmor-profiles-extraThis command installs not only the basic utilities but also additional profiles and notification support for AppArmor, enhancing its functionality.
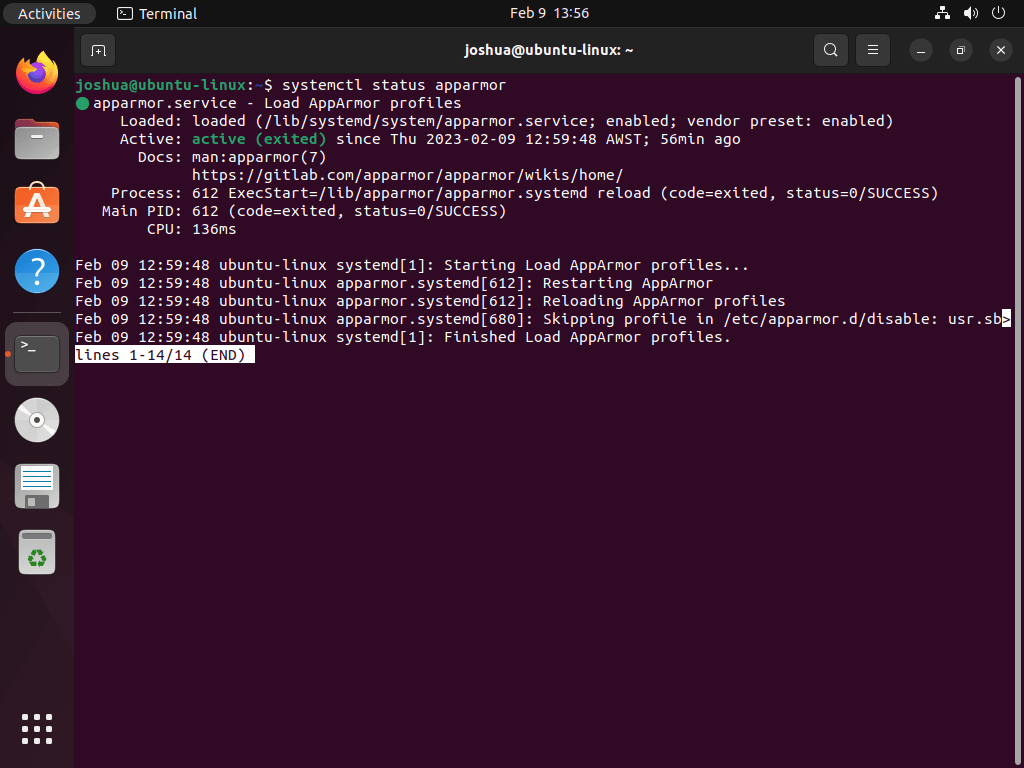
Check AppArmor Status on Ubuntu
AppArmor typically comes pre-installed and activated on Ubuntu systems. To confirm its current status, use the command:
systemctl status apparmorExample output:
Checking AppArmor’s status through systemctl ensures that the service is operational. This check is crucial as it confirms the active state of AppArmor on your system. While alternative methods exist for this verification, starting with systemctl provides a reliable and straightforward approach.
Managing Systemd Commands for AppArmor
Stopping AppArmor
To stop the AppArmor service, execute:
sudo systemctl stop apparmorDisabling AppArmor on System Boot
If you wish to prevent AppArmor from starting automatically at boot, use:
sudo systemctl disable apparmorStarting AppArmor
To start the AppArmor service, particularly after stopping it, run:
sudo systemctl start apparmorEnabling AppArmor on System Boot (Default)
To revert to the default setting where AppArmor starts at boot, execute:
sudo systemctl enable apparmorRestarting AppArmor
For changes to take effect or to reset the service, restart AppArmor:
sudo systemctl restart apparmorReloading AppArmor
To apply configuration changes without restarting the service, reload AppArmor:
sudo systemctl reload apparmorCheck AppArmor Profiles Loaded on Ubuntu 22.04 or 20.04
Reviewing Current AppArmor Profiles
Before adjusting AppArmor settings, it’s crucial to examine the status of its profiles. This is done with the apparmor_status command, which provides a detailed view of the loaded profiles and their operational modes. Use the following command in the terminal:
sudo apparmor_statusThis command outputs information such as the number of loaded profiles, profiles in enforce mode, and any associated processes. The enforce mode indicates active profiles that are currently restricting application behaviors according to their specific rules. This overview is vital for understanding the existing security posture before making any modifications.
Example output:
apparmor module is loaded.
63 profiles are loaded.
45 profiles are in enforce mode.
/snap/snapd/17883/usr/lib/snapd/snap-confine
/snap/snapd/17883/usr/lib/snapd/snap-confine//mount-namespace-capture-helper
/snap/snapd/17950/usr/lib/snapd/snap-confine
/snap/snapd/17950/usr/lib/snapd/snap-confine//mount-namespace-capture-helper
/usr/bin/evince
/usr/bin/evince-previewer
/usr/bin/evince-previewer//sanitized_helper
/usr/bin/evince-thumbnailer
/usr/bin/evince//sanitized_helper
/usr/bin/man
/usr/bin/pidgin
/usr/bin/pidgin//sanitized_helper
/usr/bin/totem
/usr/bin/totem-audio-preview
/usr/bin/totem-video-thumbnailer
/usr/bin/totem//sanitized_helper
/usr/lib/NetworkManager/nm-dhcp-client.action
/usr/lib/NetworkManager/nm-dhcp-helper
/usr/lib/connman/scripts/dhclient-script
/usr/lib/snapd/snap-confine
/usr/lib/snapd/snap-confine//mount-namespace-capture-helper
/usr/sbin/cups-browsed
/{,usr/}sbin/dhclient
apt-cacher-ng
lsb_release
man_filter
man_groff
nvidia_modprobe
nvidia_modprobe//kmod
snap-update-ns.firefox
snap-update-ns.snap-store
snap-update-ns.snapd-desktop-integration
snap.firefox.firefox
snap.firefox.geckodriver
snap.firefox.hook.configure
snap.firefox.hook.connect-plug-host-hunspell
snap.firefox.hook.disconnect-plug-host-hunspell
snap.firefox.hook.post-refresh
snap.snap-store.hook.configure
snap.snap-store.snap-store
snap.snap-store.ubuntu-software
snap.snap-store.ubuntu-software-local-file
snap.snapd-desktop-integration.hook.configure
snap.snapd-desktop-integration.snapd-desktop-integration
tcpdump
18 profiles are in complain mode.
/usr/bin/irssi
avahi-daemon
dnsmasq
dnsmasq//libvirt_leaseshelper
identd
klogd
mdnsd
nmbd
nscd
php-fpm
ping
samba-bgqd
smbd
smbldap-useradd
smbldap-useradd///etc/init.d/nscd
syslog-ng
syslogd
traceroute
0 profiles are in kill mode.
0 profiles are in unconfined mode.
3 processes have profiles defined.
3 processes are in enforce mode.
/usr/sbin/cups-browsed (1025)
/snap/snapd-desktop-integration/49/usr/bin/snapd-desktop-integration (1632) snap.snapd-desktop-integration.snapd-desktop-integration
/snap/snapd-desktop-integration/49/usr/bin/snapd-desktop-integration (1717) snap.snapd-desktop-integration.snapd-desktop-integration
0 processes are in complain mode.
0 processes are unconfined but have a profile defined.
0 processes are in mixed mode.
0 processes are in kill mode.
The output will detail the loaded profiles, showing which ones are actively enforcing security policies and which are in a more permissive complain mode. For instance, you might see profiles for network services like dnsmasq or applications like snapd. This visibility is key for system administrators aiming to maintain or enhance security measures.
Alternative Status Check: Using aa-status
Another method to check AppArmor profiles is by using the aa-status command. This offers a more in-depth look at the profiles:
sudo aa-statusThis command, similar to apparmor_status, lists all profiles and their statuses, including those in enforced, complain, and unconfined modes. Understanding these modes is essential when troubleshooting or optimizing AppArmor’s functionality.
Backing Up AppArmor Profiles
Prior to making changes to AppArmor, creating a backup of its profiles is a recommended best practice. This ensures that you can revert to a known configuration if needed. Execute the following command to back up the profiles:
sudo cp -R /etc/apparmor.d /etc/apparmor.d.bakThis command duplicates the current AppArmor profiles into a backup directory, /etc/apparmor.d.bak, safeguarding your original configuration. Having this backup is a safety net, allowing you to experiment with or modify AppArmor settings without the risk of losing your original configuration.
How to Disable AppArmor Profile on Ubuntu 22.04 or 20.04
Navigating to the AppArmor Profiles Directory
Begin by accessing the directory where AppArmor profiles are stored. This is done by navigating to /etc/apparmor.d:
cd /etc/apparmor.dListing Available AppArmor Profiles
Next, list the profiles within this directory to identify the one you intend to disable:
ls -sThis command displays all profiles stored in the /etc/apparmor.d directory. From this list, you can select the specific profile you wish to disable.
Disabling a Specific AppArmor Profile
To disable a chosen profile, use the aa-disable command. This allows you to disable individual profiles without impacting the overall functionality of AppArmor. For instance, to disable the usr.sbin.cupsd profile:
sudo aa-disable /etc/apparmor.d/<profile-name>Example of Command Execution
Executing this command will turn off the usr.sbin.cupsd profile. This action is immediate, allowing you to quickly address any issues caused by this specific profile while retaining AppArmor’s protection for other applications.
sudo aa-disable /etc/apparmor.d/usr.sbin.cupsdExample output:
Disabling /etc/apparmor.d/usr.sbin.cupsdViewing Disabled AppArmor Profiles
After disabling a profile, you can verify which profiles are currently disabled by checking the /etc/apparmor.d/disable directory:
ls /etc/apparmor.d/disableThis command provides a list of all profiles that are currently disabled in AppArmor. It’s a useful tool for monitoring and managing the profiles you’ve disabled, ensuring you have a clear record of your system’s security configuration.
How to Enable AppArmor Profile on Ubuntu 22.04 or 20.04
Re-Enabling a Disabled AppArmor Profile
In scenarios where a previously disabled AppArmor profile needs to be reactivated, the aa-enable command comes into play. This command is straightforward and restores the selected profile to its active state, ensuring its security policies are enforced once again.
Here’s how to execute this command:
sudo aa-enable /etc/apparmor.d/<profile-name>Replace <profile-name> with the actual name of the profile you intend to enable.
Example: Enabling the usr.sbin.cupsd Profile
For instance, if you previously disabled the usr.sbin.cupsd profile, the command to re-enable it would be:
sudo aa-enable /etc/apparmor.d/usr.sbin.cupsdExample output:
Setting /etc/apparmor.d/usr.sbin.cupsd to enforce mode.This command will set the usr.sbin.cupsd profile to enforce mode. Enforce mode is crucial as it dictates that the security policies defined within the profile are actively applied, thus ensuring the intended security measures are in place.
Additional Commands with AppArmor Commands on Ubuntu 22.04 or 20.04
Using the aa-genprof Command
The aa-genprof command is instrumental in generating new AppArmor profiles. It monitors an application’s system calls and crafts a profile based on this activity, which is especially useful for applications not yet covered by existing profiles.
Example: Creating a Profile for Firefox
To create a new AppArmor profile for Firefox, execute:
sudo aa-genprof firefoxThis command captures Firefox’s interactions with the system, facilitating the creation of a tailored security profile.
Applying the aa-enforce Command
The aa-enforce command is used to actively enforce AppArmor profiles. It is particularly handy after modifying profiles, as it applies new policies immediately without needing a system restart.
Example: Enforcing All AppArmor Profiles
To enforce all available profiles:
sudo aa-enforce /etc/apparmor.d/*Alternatively, enforce a specific profile:
sudo aa-enforce /etc/apparmor.d/<profile-name>Utilizing the aa-disable Command
The aa-disable command deactivates a specific AppArmor profile. When a profile is disabled, its restrictions are temporarily lifted, which can be useful for troubleshooting or granting additional permissions to an application.
Example: Disabling the Firefox Profile
To disable the Firefox profile:
sudo aa-disable /etc/apparmor.d/firefoxRemember, this change is temporary and will revert upon system reboot or AppArmor service restart.
Implementing the aa-complain Command
The aa-complain command switches a profile to “complain mode.” In this mode, AppArmor logs restricted actions instead of blocking them, aiding in testing and debugging.
Example: Switching to Complain Mode
To switch the usr.sbin.cupsd profile to complain mode:
sudo aa-complain /etc/apparmor.d/usr.sbin.cupsdReplace usr.sbin.cupsd with the desired profile name to observe its potential restrictions without enforcing them.
Executing the aa-remove-unknown Command
The aa-remove-unknown command is effective for cleaning up AppArmor profiles related to unknown or unused applications.
Example: Removing Unknown Profiles
To purge unknown profiles:
sudo aa-remove-unknownThis action streamlines your AppArmor profiles, ensuring your system maintains an organized and current security stance.
Conclusion
Throughout this guide, we’ve navigated the essential aspects of managing AppArmor on Ubuntu 22.04 or 20.04, covering how to enable, disable, and modify security profiles to suit specific needs. We delved into creating new profiles with aa-genprof, enforcing policies with aa-enforce, and even troubleshooting with modes like aa-complain. Remember, the key to AppArmor’s effectiveness lies in tailoring it to your environment. Regularly review and update your profiles to ensure they align with your security objectives and system updates. By applying these practices, you’ll maintain a robust and adaptive security posture for your Ubuntu system.